一、 Let's Encrypt
Let's Encrypt SSL 证书是一个免费的公益项目,由 Mozilla 、 Cisco 、 Akamai 、 IdenTrust 、 EFF 等组织人员发起,主要的目是为了推进网站从 HTTP 向 HTTPS 过度的进程,目前已经有越来越多的商家加入和赞助支持。
使用 Let's Encrypt 生成域名证书的前置条件:
- 拥有域名,能自主配置 DNS 记录。或者提供 web 服务器验证,需要在网站目录下放一个文件,推荐第一种方式。
- 获取证书的环境要能访问到 DNS 服务器,因为中途需要校验 DNS 解析。
- 拥有主机的超级权限,中途需要更新和安装组件。
二、申请流程
第一步:拉代码,代码开源于 Github 。
|
1 2 3 4 5 6 7 8 |
> git clone https://github.com/letsencrypt/letsencrypt Cloning into 'letsencrypt'... remote: Enumerating objects: 29, done. remote: Counting objects: 100% (29/29), done. remote: Compressing objects: 100% (27/27), done. remote: Total 61424 (delta 7), reused 4 (delta 2), pack-reused 61395 Receiving objects: 100% (61424/61424), 20.12 MiB | 5.01 MiB/s, done. Resolving deltas: 100% (44625/44625), done. |
完成后执行命令生成证书:
|
1 2 3 |
./certbot-auto certonly -d *.maqian.art --manual \ --preferred-challenges dns \ --server https://acme-v02.api.letsencrypt.org/directory |
解释一下各个参数的含义:
certonly: 表示当前为安装模式--manual: 表示手动安装插件,不要自动安装了--preferred-challenges dns: 校验方式为 dns 验证-d *.maqian.art: 要生成的域名列表,可以为多个,如果是多个分别以-d 加上即可--server: Let's Encrypt ACME v2 版本使用的服务器
接下来的步骤一直接受即可,直到出现添加 DNS 记录为止:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 |
Requesting to rerun ./certbot-auto with root privileges... [sudo] password for ma: Saving debug log to /var/log/letsencrypt/letsencrypt.log Plugins selected: Authenticator manual, Installer None Enter email address (used for urgent renewal and security notices) (Enter 'c' to cancel): maqian@dyxmq.cn - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Please read the Terms of Service at https://letsencrypt.org/documents/LE-SA-v1.2-November-15-2017.pdf. You must agree in order to register with the ACME server at https://acme-v02.api.letsencrypt.org/directory - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - (A)gree/(C)ancel: A - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Would you be willing to share your email address with the Electronic Frontier Foundation, a founding partner of the Let's Encrypt project and the non-profit organization that develops Certbot? We'd like to send you email about our work encrypting the web, EFF news, campaigns, and ways to support digital freedom. - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - (Y)es/(N)o: Y Obtaining a new certificate Performing the following challenges: dns-01 challenge for sinfor.maqian.io - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - NOTE: The IP of this machine will be publicly logged as having requested this certificate. If you're running certbot in manual mode on a machine that is not your server, please ensure you're okay with that. Are you OK with your IP being logged? - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - (Y)es/(N)o: Y - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Please deploy a DNS TXT record under the name _acme-challenge.maqian.art with the following value: zw1MeEkmGZOqSqiySp9Ke8S5a9BXC3O4tYzlbjwU-CU Before continuing, verify the record is deployed. - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Press Enter to Continue |
此时需要在 DNS 服务商处添加 dns 解析,记录类型为 TXT,记录为_acme-challenge,值为 zw1MeEkmGZOqSqiySp9Ke8S5a9BXC3O4tYzlbjwU-CU 。当 DNS 记录设置好后,新开一个终端查询解析是否生效:
|
1 2 3 4 5 6 7 8 |
> nslookup -type=txt _acme-challenge.maqian.art Server: 100.100.2.136 Address: 100.100.2.136#53 Non-authoritative answer: _acme-challenge.maqian.art text = "zw1MeEkmGZOqSqiySp9Ke8S5a9BXC3O4tYzlbjwU-CU" Authoritative answers can be found from: |
当查询到的记录和给定的都一致之后按下任意键执行下一步,如果 DNS 验证成功就会出现以下信息:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 |
Waiting for verification... Cleaning up challenges IMPORTANT NOTES: - Congratulations! Your certificate and chain have been saved at: /etc/letsencrypt/live/maqian.art-0001/fullchain.pem Your key file has been saved at: /etc/letsencrypt/live/maqian.art-0001/privkey.pem Your cert will expire on 2019-03-22. To obtain a new or tweaked version of this certificate in the future, simply run certbot-auto again. To non-interactively renew *all* of your certificates, run "certbot-auto renew" - If you like Certbot, please consider supporting our work by: Donating to ISRG / Let's Encrypt: https://letsencrypt.org/donate Donating to EFF: https://eff.org/donate-le |
此时就表示证书已经申请完成了,存放的路径为:/etc/letsencrypt/live/maqian.art-0001 。
|
1 2 3 4 5 6 7 |
> sudo ls /etc/letsencrypt/live/maqian.art-0001/ -l total 4 lrwxrwxrwx 1 root root 39 Dec 22 23:46 cert.pem -> ../../archive/maqian.art-0001/cert1.pem lrwxrwxrwx 1 root root 40 Dec 22 23:46 chain.pem -> ../../archive/maqian.art-0001/chain1.pem lrwxrwxrwx 1 root root 44 Dec 22 23:46 fullchain.pem -> ../../archive/maqian.art-0001/fullchain1.pem lrwxrwxrwx 1 root root 42 Dec 22 23:46 privkey.pem -> ../../archive/maqian.art-0001/privkey1.pem -rw-r--r-- 1 root root 692 Dec 22 23:46 README |
三、安装到 nginx
上面一共生成了四个文件,各自的用途为:
cert.pem: Apache 服务器端证书chain.pem: Apache 根证书和中继证书fullchain.pem: Nginx 所需要 ssl_certificate 文件privkey.pem: 安全证书 KEY 文件
部署到 nginx 只需要添加一下指令即可:
|
1 2 3 |
ssl on; ssl_certificate /etc/letsencrypt/live/maqian.art-0001/fullchain.pem; ssl_certificate_key /etc/letsencrypt/live/maqian.art-0001/privkey.pem; |
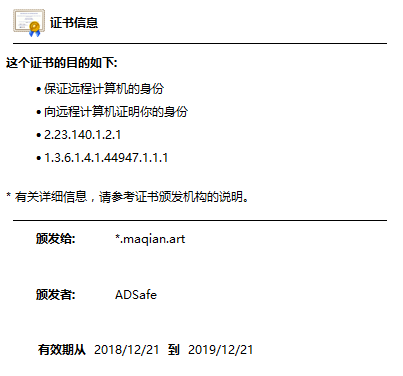
打开网站,点开左上角地址栏的 https,查看证书:



评论